Introducing RealONE from RealVNC
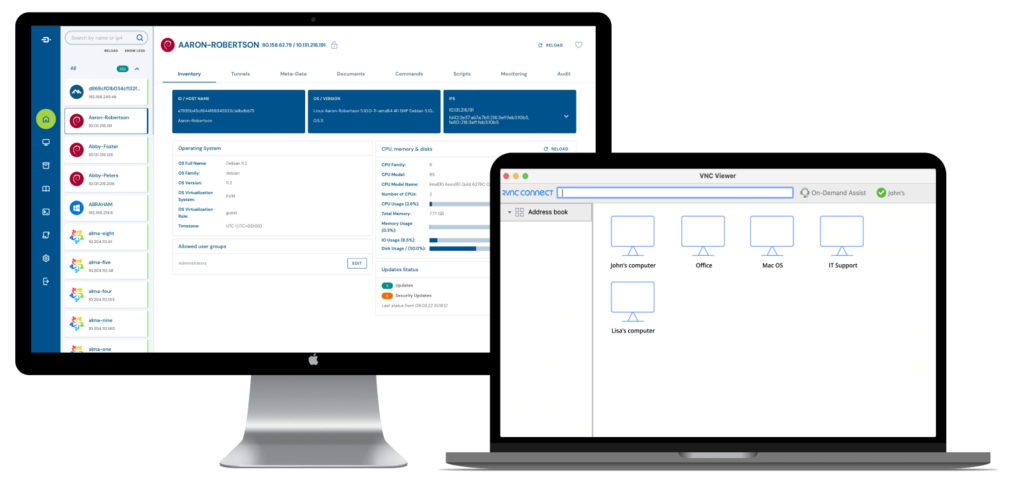
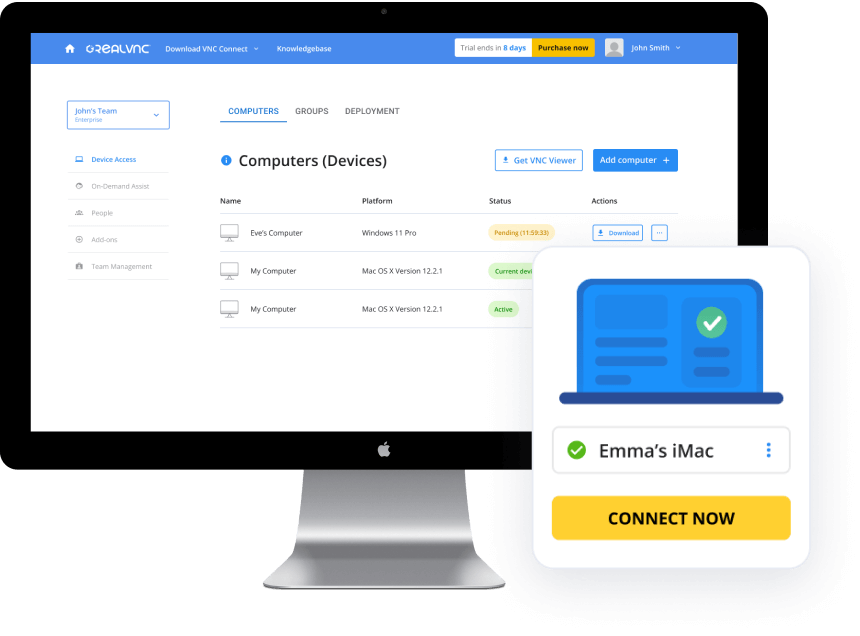
Effectively monitor, manage and support your IT systems with the combined might of RPort’s remote management tools and RealVNC Connect’s remote access solutions.
With the release of RPort 1.0, we have ended development and support for the open source version of the solution. Instead, RPort is now available for purchase as RealONE – a commercial bundling of RPort and RealVNC Connect that brings together the combined capabilities of both solutions.
Administer your IT network
effectively and securely,
regardless of complexity.
From monitoring device health, deploying updates, scheduling scripts, and readily accessing remote systems and equipment, RealONE helps you more effectively and securely administer your IT network, regardless of complexity.

Features for RPort:
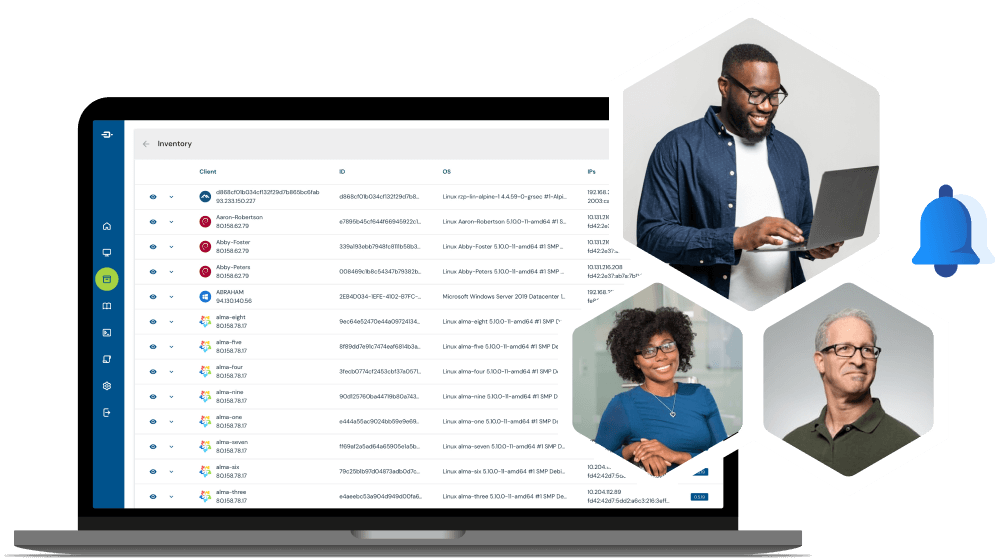
- Efficient IT Infrastructure Management: You can manage your entire IT infrastructure from your browser, command line or REST API.
This includes servers, routers, switches, printers, IoT devices and more, all from a single dashboard.
- Secure Remote Login: RPort enables secure login into any Windows or Linux Server without a public IP address and manages IoT devices from anywhere without a VPN.
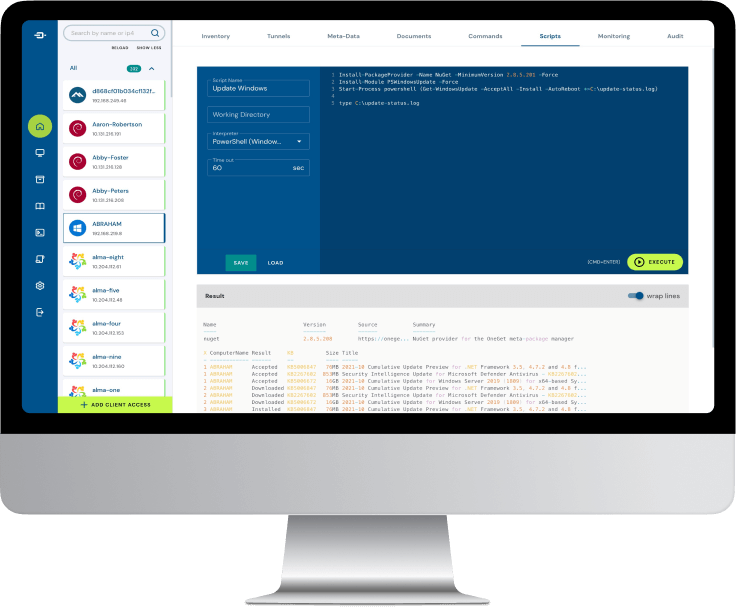
- Command & Script Execution: You can run remote commands directly from your browser on one or more servers. Additionally, you can store, manage, and reuse scripts in a library, schedule them to run later or periodically, and share script-based solutions with team members.
- High Security: RPort meets high-security requirements with features like two-factor authentication, AES encryption using SSH tunnelling, and prevention of man-in-the-middle attacks.
- Self-Hosting Options: Run your own RPort server for complete control over your data and systems for increased security. Your data stays on your network, and you can choose to host your RPort server
on-premise or in the cloud.
Features for RVNC Connect:
- Choice of connectivity: Our cloud-brokered connections offer simple and secure over-the-Internet access, while our direct (IP) connectivity lets you deploy on local networks for those super sensitive environments.
- Multi-platform support: Consolidate tools with a single remote access solution that supports all the major desktop and mobile operating systems.
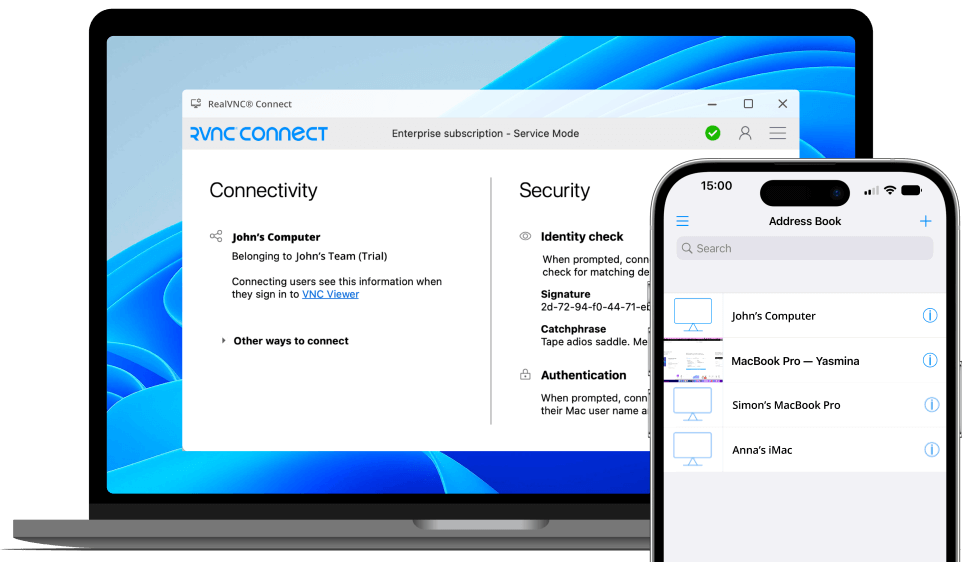
- True Zero Trust: Ensure the right people have the right access with a suite of MFA options and granular user and session permissions across your entire account.
- Deploy at scale: License your RealVNC Servers in one go using GPO or MSI, while our API makes ongoing admin easy with automated device management.
- PLUS: On-Demand Assist for rapid remote support: Deliver rapid,
just-in-time remote support to anyone without any user-side configuration or install required at all.

